A hacked WordPress website can cause damage to your revenue, reputation, and brand. If your website is a crucial part of your business, then you need to start paying extra attention to your WordPress website security. This post will cover the best WordPress website security practices that will improve your WordPress security and keep your site safe from hackers and malware.
Security is about risk reduction, not risk elimination.
Being open source is not the main problem about WordPress. The popularity of WordPress makes it attractive to website hackers. Hackers aim to take away your visitors, SEO rankings, and server resources – regardless of the size of your website. The good news is that you can totally keep your WordPress website secure with effective maintenance and administration.
Free up some time in your busy life, by handing over your website worries to us! Quick and efficient WordPress support and maintenance, with WPCruiseControl now at your order!
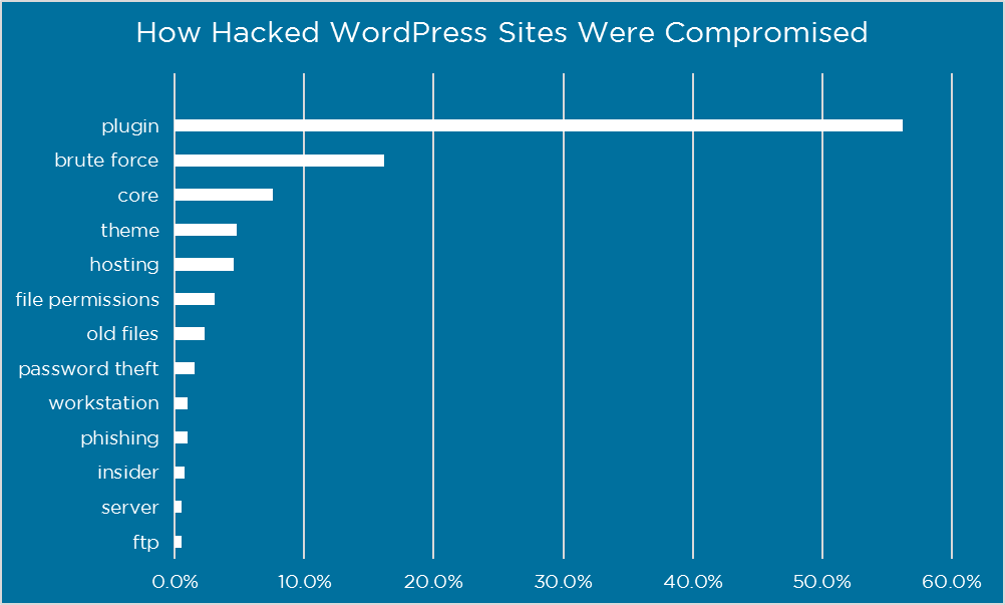
Image Source: WordFence
How? You ask?
Follow our complete guide below for The Top 65 Most Effective WordPress Website Security Practices and prevent yourself from getting hacked. Here Are 65 Steps To Ensure Your WordPress Website Is Clean, Secure And Hack-Free!
Basic WordPress Security Checks
1. Secure your working environment by making sure your local computer, browser, and routers are up-to-date, free of spyware, malware, and virus infections.
2. Consider using tools like no-script in your browser and VPN’s to encrypt your online communication when moving between locations and using different public WiFi hotspots.
3. The web server running WordPress can have vulnerabilities. If you are managing your own server, make sure that you install security updates for your operating system, web server, PHP, and applications. Or get someone qualified to do it.
4. When connecting to your server you should always use an SFTP connection.
5. If you run multiple blogs on the same server, it is wise to consider keeping them in separate databases each managed by a different user.
Frontend – Login Page and Passwords:
6. Do not use admin as your username. Create a new user in WordPress at Users > New User and make that a user with Administrator rights. After that, delete the admin user.
7. Using an email ID instead of a username to log in is a more secure approach. Usernames are easy to predict, while email IDs are not.
8. You can also customize the login page URL and the page’s interaction. When hackers know the direct URL of your login page, they can try to brute force their way in.
9. Use a less common password. You can use tools like iPassword and Lastpass to generate passwords. They are more effective.
10. Always use the CLU Rule while creating passwords. CLU: Complex. Long. Unique. Change your website passwords regularly. Improve their strength by adding uppercase and lowercase letters, numbers, and special characters.
11. Add a two-factor authentication (2FA) to reduce the risk of Brute Force attacks.
12. Use tools like Google Authenticator and Rublon Plugin to add a two-factor authentication.
13. Limit login attempts. Brute force attacks generally target login forms. Limiting login attempts will clear off this vulnerability. You can use security plugins like the iThemes Security Plugin to specify a certain number of failed login attempts after which the plugin bans the attacker’s IP address.
14. A lockdown feature for failed login attempts can also solve a huge problem. Whenever there is a hacking attempt with repetitive wrong passwords, the account gets locked, and you get notified of this unauthorized activity.
15. You could also limit the number of attempts to login from a certain IP address. Plugins like the All in One WP Security & Firewall have options to simply change the default URL (/wp-admin/) for a login form.
16. Deal rightly with multiple people accessing your admin panel. Don’t give applications or users access beyond what they need. Only give permissions to users or applications when they need it. Assign people to appropriate roles, and you’ll greatly reduce your security risk.
17. Automatically log out Idle Users in WordPress. Logged in users can sometimes wander away from the screen, and this poses a security risk.
18. You can do this with the help of Idle User Logout Plugin. Simply set the time duration and uncheck the box next to ‘Disable in wp-admin’ option for better security.
19. Another tricky method to increase security is by adding a security question to your WordPress login screen. You can add security questions by installing the WP Security Questions plugin as well.
20. Ensure to delete any unused or unknown user accounts.
Backend – Files and Folders:
21. The wp-admin directory is the heart of any WordPress website. Password-protect the wp-admin directory to keep it safe and secure. This way the website owner may access the dashboard by submitting two passwords. One protects the login page, and the other the WordPress admin area.
22. AskApache Password Protect plugin automatically generates a .htpasswd file, encrypts the password and configures the correct security-enhanced file permissions.
23. Implementing an SSL (Secure Socket Layer) certificate is one smart move to secure the admin panel. SSL ensures secure data transfer between user browsers and the server, making it difficult for hackers to breach the connection or spoof your info.
24. The SSL certificate also affects your website’s rankings at Google. Google ranks sites with SSL higher than those without it.
25. Turn off PHP error reporting.
26. Hide wp-config.php and .htaccess. For better WordPress security, you’d need to add this to your .htaccess file to protect wp-config.php:
<Files wp-config.php>
order allow, deny
deny from all
</Files>
27. The wp-config.php file holds crucial information about your WordPress installation and is the most important file in your site’s root directory. Take your wp-config.php file and move it to a higher level than your root directory to make it inaccessible to hackers.
28. And don’t worry, even if it is stored one fold above the root directory, WordPress can still see it.
29. Use WordPress security keys, set of random variables, for authentication to improve security (encryption) of information in cookies. The Sucuri Plugin can help you with WordPress security keys.
30. Disable File Editing via editor in WordPress. This is the easiest way a hacker could change your files. The editor is accessible to anyone who logs into your account. It just takes a line of code to avoid this problem. Open your wp-config.php file and paste the following code:
define( ‘DISALLOW_FILE_EDIT’, true );
31. XML-RPC helps in connecting your WordPress site with the web and mobile apps. But because of its powerful nature, XML-RPC can significantly amplify the brute-force attacks. Be selective on how and what you allow the XML-RPC to access. And if you are not using the XML-RPC, it is highly recommended that you disable it.
32. Using the default wp- table prefix makes your site database prone to SQL injection attacks. Such attack can be prevented by changing wp- to some other term, e.g. you can make it mywp-, wpnew-, or anything that you want. Plugins like WP-DBManager or iThemes Security can help you do the job with just a click of a button.
33. Set directory permissions carefully, especially if you’re working in a shared hosting environment.
34. Setting the directory permissions to “755” and files to “644” protects the whole filesystem – directories, subdirectories, and individual files.
35. This can be done either manually via the File Manager inside your hosting control panel, or through the terminal (connected with SSH) – use the “chmod” command.
36. Disable directory listing with .htaccess.
37. If you create a new directory as part of your website and do not put an index.html file in it, your visitors can get a full directory listing of everything that’s in that directory.
38. You can prevent this by adding the following line of code in your .htaccess file:
Options All -Indexes
Don’t forget to save and upload .htaccess file back to your site.
39. Delete any old WordPress installations or directories. Anything that is old and unused lying in your directories can eventually be found by hackers and used to gain access to your site. So delete them!
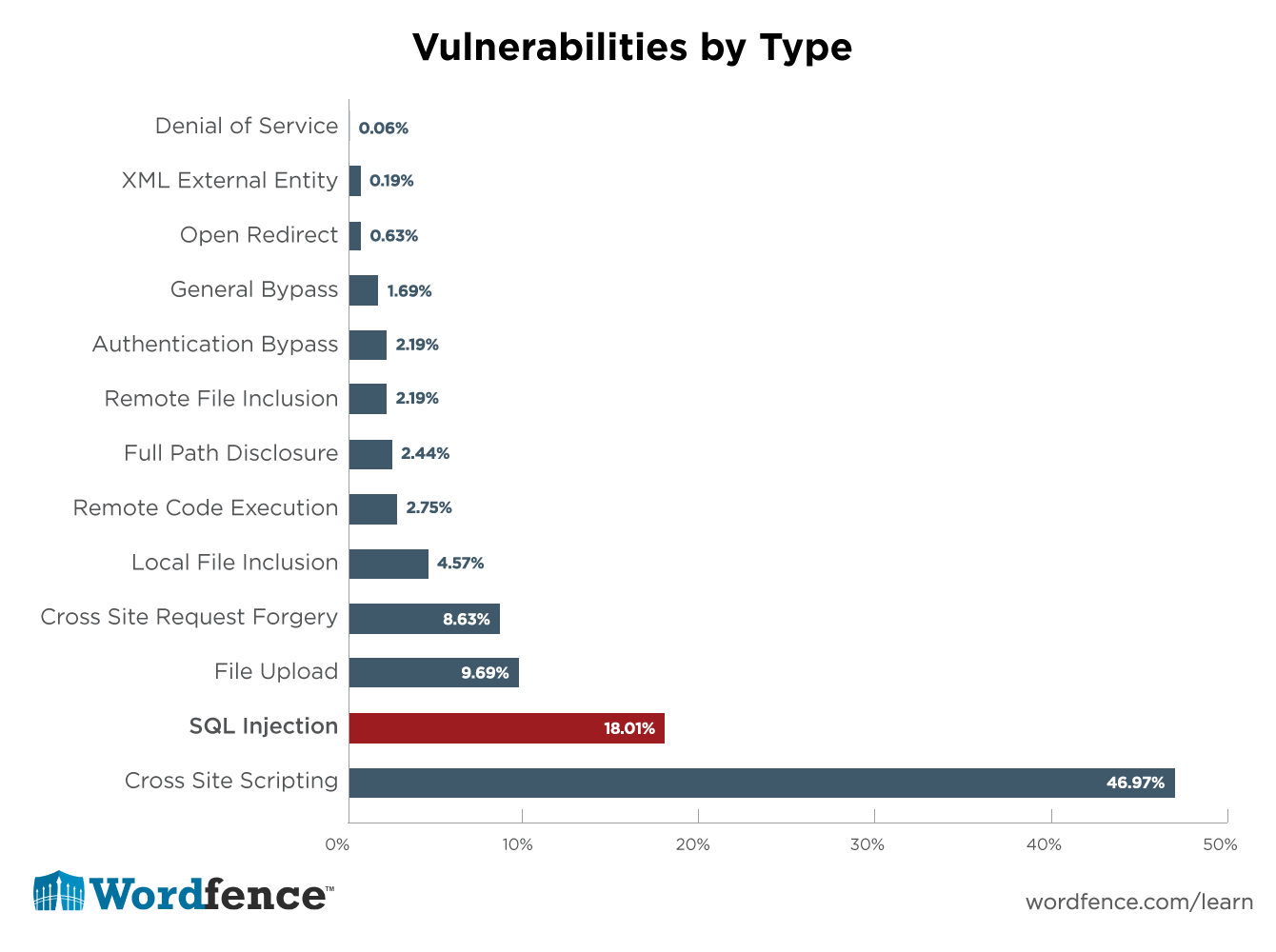
Image Source: WordFence
WordPress Website Hosting & Backup:
40. Be very careful about the hosting you choose. The cheapest solution can sometimes turn out to be too expensive on you later.
41. Using a Managed WordPress hosting service provides a more secure platform for your website. Managed WordPress hosting companies offer automatic backups, automatic WordPress updates, and more advanced security configurations to protect your website.
42. Website owners are allowed to install and configure as many websites as they want in Shared Hosting. In many instances, a website is compromised via a concept known as cross-site contamination in which a neighboring site is used as the attack vector. Avoid having a large number of diverse web applications on a single hosting account.
43. One way to account for this is to create two accounts, one which you treat as a production environment – only live sites are published – and a staging one, in which you put everything else. Always test updates in a staging environment before pushing it to production.
44. All of your site’s data and information is stored in the database. You need to make sure your website is backed up regularly.
45. You must regularly save full-site backups to a remote location (not your hosting account). You could use a cloud service like Amazon, Dropbox, or private clouds like Stash.
46. Keeping an off-site backup is perhaps the best antidote. If you have a backup, you can always restore your WordPress website to a working state any time you want.
47. Set strong passwords for your database.
Updates To The WordPress Core, Plugins And Themes:
48. Staying up to date is crucial. Many hackers rely on the mere fact that people can’t be bothered to update their plugins and themes. A very large percentage of the website hacks come from out-of-date, vulnerable, versions of plugins.
49. The easiest way to protect your website is to employ a firewall. They virtually patch up and harden your website at the edge.
50. Free plugins and themes could be a possible vulnerability. When adding a plugin/theme always check the rating and number of ratings of that plugin.
51. Sucuri strongly recommends against using any plugins that haven’t been updated for a long time.
52. Do not get plugins/themes from sources that are not trusted. Malicious people and organizations distribute what is known as ‘nulled‘ plugins and themes which contain malicious code that will extend the premium plugin, but bundle it with malware.
53. Be ruthless when it comes to plugins. If you can do without the functionality that plugin offers, deactivate it and remove it.
54. Subscribe to the vulnerability database maintained by WPVulnDB.com. You can also stay ahead of the latest trends following WordPress’s own Security tag.
55. Remove your WordPress version number. If the hackers know which version of WordPress you use, it’s easier for them to tailor-build the perfect attack. You can hide your version number with almost every security plugin.
56. Delete any themes, plugins or extensions that you no longer use or haven’t been updated in a long time.
57. If you have a custom theme designed for your WordPress website you should be maintaining any custom software uploaded with it as well.
Read How Updating WordPress Plugins Can Secure Your Website From Hackers On Our Blog!
Auditing & Monitoring:
58. Set up an auditing and monitoring system that keeps track of everything that happens on your website including file integrity monitoring, failed login attempts, malware scanning, etc. You can use plugins like Wordfence, or iThemes Security. Monitoring file system changes can give you early warning of an intrusion.
59. Logical separation of applications into separate accounts with their own access will confine a compromise to that one account and reduce damage.
60. The idea of Defense of Depth subscribes to the concept that there is no single solution capable of addressing all your security concerns. It promotes the use of a layered approach to complementary security solutions each designed to address each other’s shortfalls.
61. Deploy tools that allow you to maintain visibility into the overall security state of your site.
62. Security through obscurity is a complementary layer to a Defense in Depth approach to security, it should not be the strategy.
63. Removing the mentioning of “Powered by WordPress” tag from the frontend of your website will not make it apparent to the hackers. Although this isn’t completely necessary, it can be a safety measure.
64. Getting Professional WordPress help to take care of your site is one of the best practices. We can do just that for you!
65. Allowing a professional security company like Sucuri to fix your website will ensure that your site is safe to use again. It will also protect you against any future attacks.
Final Words:
According to WP Scan, a black box WordPress vulnerability scanner, there are have been 4618 vulnerabilities (2,355 unique) reported to date. 52% of the vulnerabilities reported were WordPress plugins. WordPress core accounts for 37% and WordPress themes account for 11%.
As you can see there are probably a lot more security vulnerabilities than you even thought! Which means you are always at risk of being attacked or hacked. You can never prevent these things from happening 100% of the time.
Like we mentioned before, Security isn’t about risk elimination, it is about risk reduction. Your system should be configured to minimize the amount of damage that can be done in the event that it is compromised. And the best thing you can do is to implement the best security practices to protect yourself.
With multiple layers of security, if one fails you may still stop the attack, or at the very least be able to detect it early and recover quickly.
Have we missed any? Have any other methods worked for you!? Let us know in the comments below!